Multi-Cloud Networking
Seamless connectivity across clouds
Gain complete connectivity on a mesh network across any cloud providers, on-premises solutions, and Kubernetes clusters—without toggling between VPNs.

Trusted by 10,000+ global companies
Develop and deploy to any cloud provider across regions
Bring all cloud providers you use under one network—Google’s GCP, Amazon’s AWS, Microsoft’s Azure, or whatever it may be.
Simplify SSH access on every cloud provider
Seamlessly SSH into any resource in the cloud or on-prem, without needing to create, rotate, or revoke keys.
Enable cross-cluster communication
Connect clusters in different orchestration platforms like Kubernetes, ECS, and EKS, and provide policy enforcement across resources in each cluster.
Uniform connectivity across any cloud provider
Securely connect data lakes, cloud resources, and more
Direct end-to-end encryptions with WireGuard across clouds mean no more bastions, VPN gateways, public exposure, or workflow compromises. Create a more performant and responsive development environment.

Make managing multiple clouds easy
Replicate infrastructure across clouds and regions easily to enable low-latency, fault-tolerant, high-throughput, always-available access.
A zero-trust overlay network to connect any cloud

Optimize resource availability
Achieve the high availability, load-balancing, and failover capabilities your project needs at a global scale with regional routing.
Split tunneling
Easily determine which traffic should flow through your overlay network and the public internet to ensure optimal performance and low latency for developers.
Fine-grained access control
Leverage user and machine identity to institute least-privilege access across your network infrastructure, restricting access based on job, role, or function.
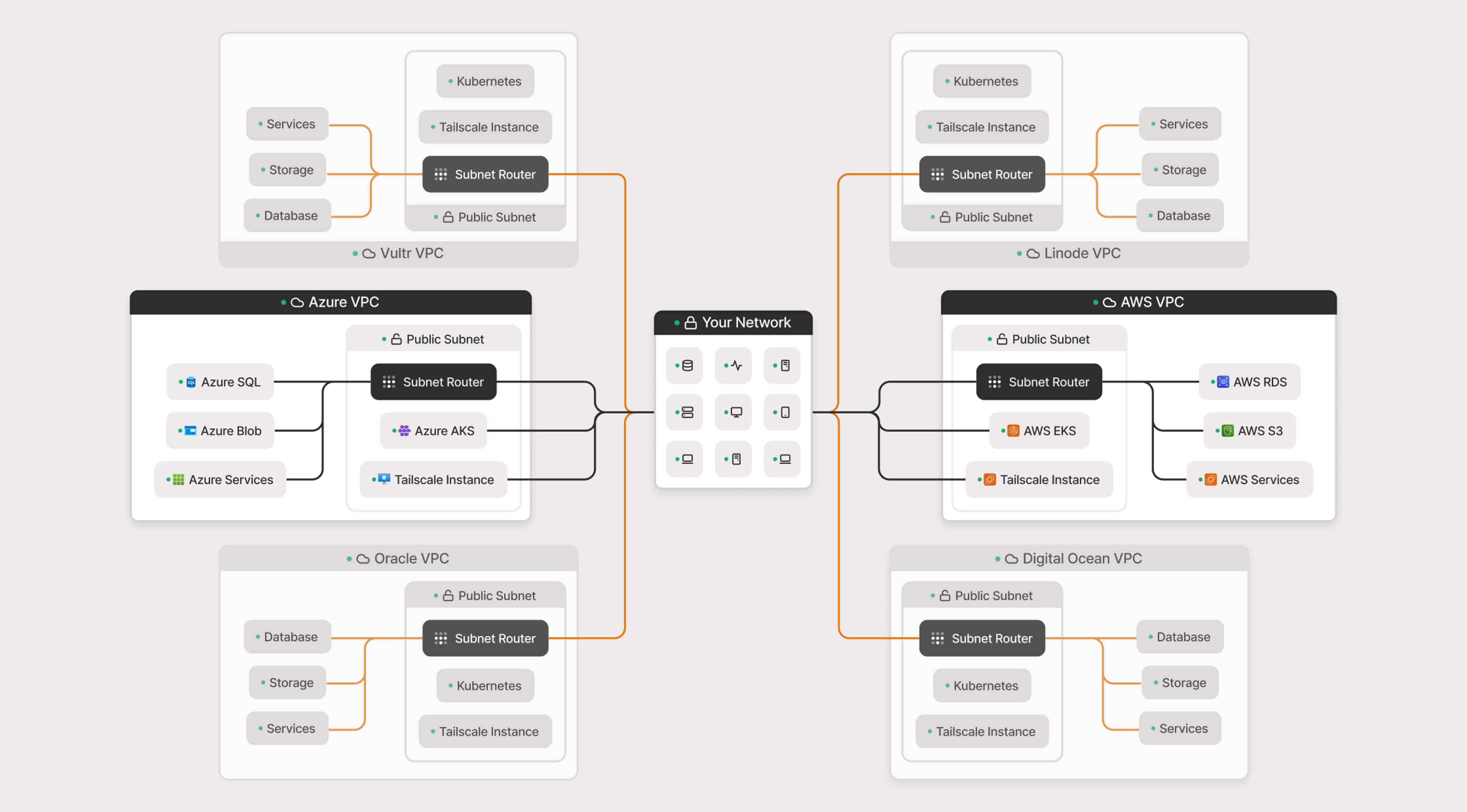
Subnet Routers
Connect entire VPCs hosted on any cloud platform, and extend your private network to devices where you cannot install Tailscale directly.
Pricing that works for everyone
For individuals who want to securely connect personal devices, for free.
For small teams seeking an easy-to-use and quick-to-deploy secure network access solution.
For growing teams seeking advanced service/resource-level networking and identity-aware access controls.
For organizations seeking advanced user and posture management, robust compliance, and dedicated support.
Frequently asked questions
Over 9,000 Engineering & IT teams use Tailscale’s networking software to secure their work from anywhere, reduce developer disruption, and protect critical infrastructure. Want to learn more? Read our frequently asked questions, or talk to a member of our team.
Can Tailscale integrate with our identity provider?
Yes! Tailscale supports major identity providers (IdPs) like Okta, Google Workspace, Microsoft Entra ID (formerly Azure AD), and others. You can enforce authentication with SSO and MFA for secure, seamless access.
Will Tailscale slow down my network?
No, Tailscale is optimized for speed. Because it establishes direct, peer-to-peer connections whenever possible, it avoids the bottlenecks and congestion that come with traditional VPN gateways.
